Contractors
Mitigate Data Risk From Contractors & Third Parties
Contractors are a key part of the workforce and they need access to critical data to get their work done. Easily prevent them from sharing information outside of your organization with Code42 Incydr™.
Connect With Sales
The Problem
Contractors need access to critical company data – without fear of it being shared
Organizations in every sector depend on contractors and vendors provide temporary help. However, third parties with authorized access to company data are a significant insider threat. What makes contractors a higher risk for data exfiltration?
Use of personal devices
Connecting to networks with personal devices and using unsanctioned apps create blind spots in data security posture.
Differing work cultures
Third-party employees will operate with different security standards – increasing the risk of negligent data leaks as well as intentional data theft.
Industry employment
Contractors and consultants who stay within the industry heighten the risk of exfiltrating your proprietary data to other competitors.
The Solution
Stop data leaks and reduce your risk exposure with Incydr
Code42 Incydr provides a comprehensive understanding of data exposure from contractors and other third-party employees. It alerts on which activities require security intervention and blocks unacceptable data exfiltrations.
Incydr is built for monitoring & responding
to third-party data risks
What makes Incydr stand out?
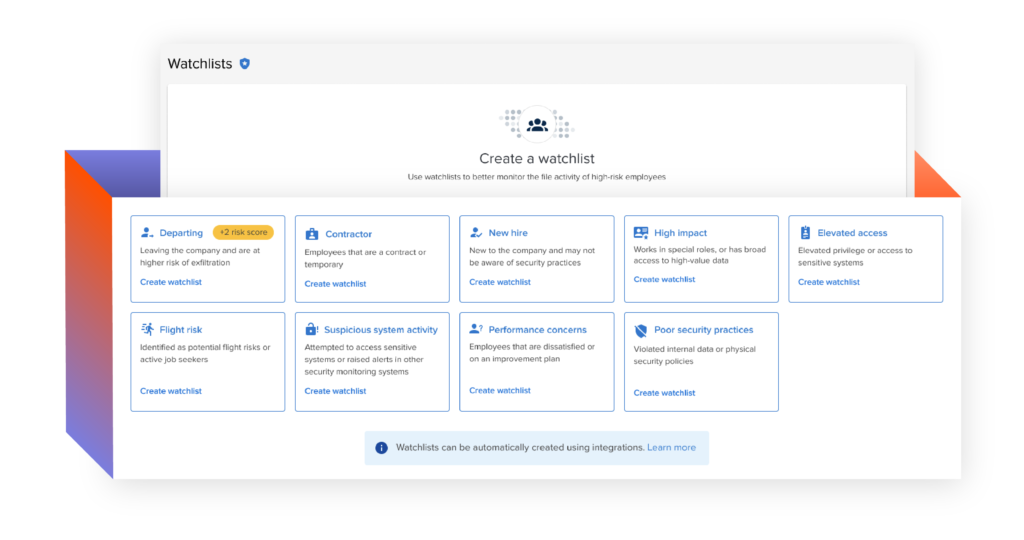
Add contractors to a Watchlist for enhanced Incydr data activity monitoring
Detect all file sharing and exfiltration through an endpoint agent and direct cloud & email integrations
Implement real-time blocking for contractors on a Watchlist when file sharing is unacceptable
Our customers protect their critical data from leaving behind their back
Let us show you how they see and stop data leaks with Incydr and Instructor.
Connect With Sales
Departing Employees
Most employees take data with them when they leave for their next job. We make sure your most valuable files stay with you.
Learn MoreRepeat Offenders
Behind every data risk event is an employee who likely didn’t follow the rules – again. Stop data exfiltration from users who violate security policies.
Learn MoreRemote Workforce
Remote workers introduce new security challenges. We help you manage the risk of off-network activity when employees work from home.
Learn More