How do you summarize three days of jam-packed security sessions (150+ to be exact) to 5 key takeaways? Especially when those sessions address challenges most critical to security and risk management leaders. In my case, I get to look at them strictly through an Insider Risk Management (IRM) vernacular so that makes it slightly easier. For starters, and on a personal note, it felt great to be around people again, not the kind that live in a Zoom or WebEx box, real people. Conferences are back, with a bang!

Before I get to my 5 takeaways, I do want to set the stage a little with Gartner’s keynote on the opening day. As a sci-fi fan myself, I understood the angle of being transported to 2032 and leveraging AI to fight threats, vulnerabilities and risks that organizations will no doubt encounter. My fear walking out of the keynote is how much of the focus remains on external threat vectors alone. I asked myself, where’s the insider risk scenario in all of this? Luckily, the Gartner sessions made up for that miss. Mainly led by Gartner analysts Paul Furtado (VP Analyst,Gartner) and Andrew Bales (Principal Analyst, Gartner), these sessions covered a range of topics that I will attempt to summarize into 5 takeaways.
INSIDER RISK WAS A THEME AT THE CONFERENCE (DIRECTLY & INDIRECTLY)
Even if you take Code42 out of the mix, I will note that Gartner had a number of sessions that directly addressed the topic (A New Look at Insider Risk, Protection From the Risk Within: Managing Insider Risk – both led by Paul Furtado). Additionally, it was interesting to note how insider risk had also become a talking point within broader data security considerations. Nathan Hunstad (Deputy CISO, Code42) added “How IRM Enables Data Security by Uniting Security and Employees” to the agenda mix to provide a more real-world perspective on what Code42 was seeing from its own customers. Microsoft joined the IRM party too with tracks dedicated to the topic. Yes, a lot of people are talking about it!
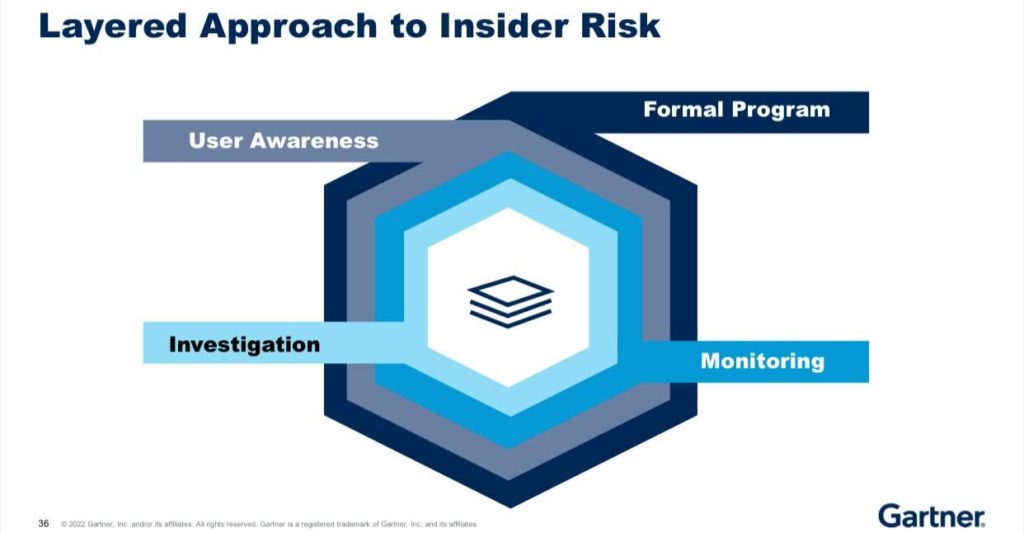
IRM IS A PROGRAM, NOT A PRODUCT
I was fascinated by the number of times a clarification had to be made between a security category and a product. There is definite confusion in the market! We 100% agree that IRM is a program and have been saying so from the beginning. It was encouraging to see acknowledgement that this program is rooted in transparency, training and technology. This is a layered approach and while the notion of any program may appear scary, attendees were relieved to hear that they can kick off this program with little to no cost – start by making your employees aware through transparency.
SECURITY AWARENESS IS KEY
Paul Furtado (VP Analyst,Gartner) joked about the number of times he referenced “security awareness” in his presentations (about 42 by my count). All jokes aside, organizations definitely realize the value of empowering their workforce with security education. The caveat though is the delivery mechanism of the educational moment. How organizations choose to deliver their security awareness and when is critical to employee engagement and retention. The tally of “security awareness” mentions was definitely up to 100 by the time Nathan Hunstad (Deputy CISO, Code42) took the stage to deliver his session appropriately titled “How IRM Enables Data Security by Uniting Security and Employees”.

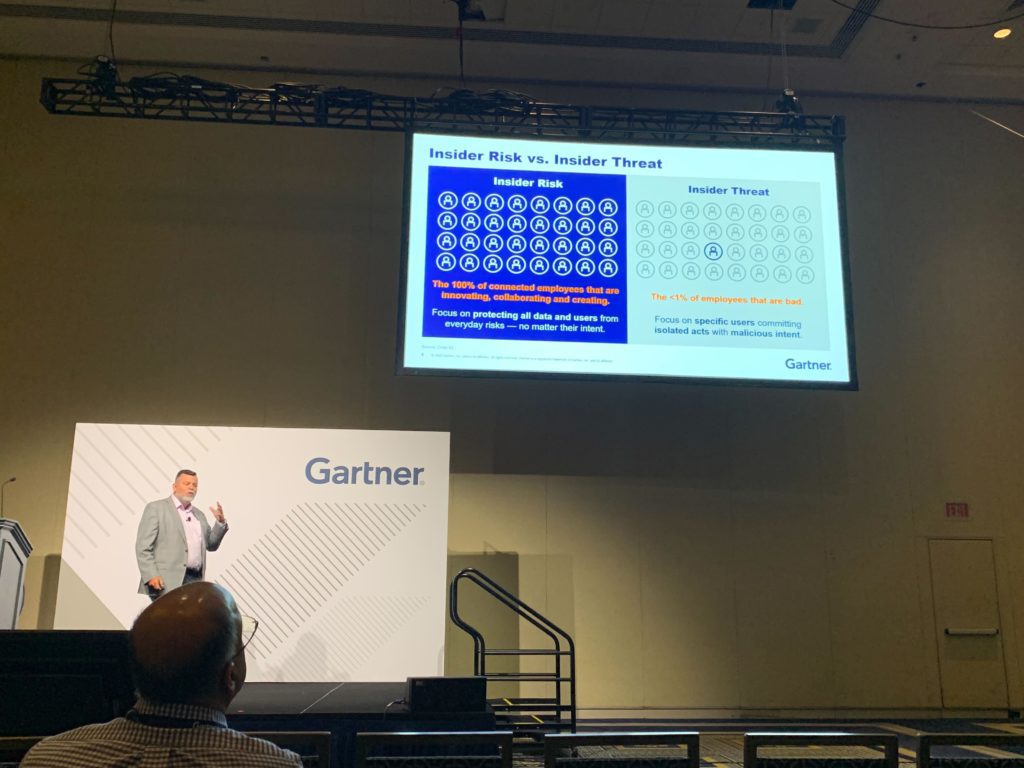
DLP IS NOT A PRODUCT. IT IS A CONCEPT COMPANIES NEED TO SOLVE
This one stuck with me especially since many customers are either contemplating a DLP solution or more often, looking for alternatives. What struck me here is the “problem” organizations are looking to solve – data loss or data leak. Whether malicious or accidental, the problem organizations are looking to solve is their data or IP going out into the wild. In the case of DLP, there is a viable control mechanism to potentially stop something. But is this truly preventative? I’d argue it’s reactive – assuming it even works. As Paul likes to quote “Not every insider risk leads to an insider threat but you better believe every insider threat started off as an insider risk!” Context Matters! And when you have sessions titled “Is Data Loss Prevention Still Worth the Price of Protection?”, it’s fair to surmise this discussion will only continue.
THE RIGHT METRICS BRING IRM TO THE BOARDROOM AND C-SUITE
For all the talk and fascination with dashboards and UIs, this was a reality check. Dashboards mean absolutely nothing if they’re not speaking the language of your C-suite. The top tips shared reporting to business leaders followed the following model courtesy of Lisa Neubauer (Director Advisory, Gartner):
- Link to business objectives
- Provide context
- Tell a story
- Limit the quantity of data points, but improve the quality
- Use metrics to drive action. Be prescriptive!
Insightful? I certainly thought so. There is really no such thing as “stupid simple” as long as you understand the language of your audience. Operational Metrics are geared to security teams whereas Business Metrics are tied to business leaders – to equip them to make decisions!
BONUS TAKEAWAY: CODE42 AND MICROSOFT BOTH OFFER IRM. APPROACHES MAY VARY
This is a key consideration for organizations as they explore the myriad of IRM solutions that are vying for attention and budget. At the root of IRM is the culture you want to instill and while Code42 always leads with and promotes empathy, the Microsoft approach appears more rooted in scrutiny and consequence. Don’t get me wrong, they’re both important but organizations need to remind themselves that employees (the end users) are sensitive to the degree of “big brother” you choose to go to so transparency and empathy just may be your path.
In summary, this was a great event with insightful sessions. It was great to experience the rush, chaos and enthusiasm that comes with exhibitor halls too. For once, I appreciated the experience of being sold to. Here’s hoping for many more conferences (in-person) to come!
Incydr’s Approach
Respond confidently to data theft before damage is done
Incydr, a data protection solution, allows security teams to detect data theft by monitoring cloud & endpoint exfiltration, and accurately tailor responses to each offense. Let’s work together to protect IP without disrupting users or causing more work for your security team.
Discover Incydr