With all the alerts coming from data security tools, how much information is too much information? What if security teams could zero in on the insider risks that pose the biggest threats, and prioritize which ones to investigate? How could the modeling of typical activity for individual users without admin inputs cut unnecessary investigations to save them time?
Joe Payne, Code42’s president and CEO explains how we are helping to solve these insider risk detection and investigation challenges. “Cybersecurity teams are drowning in alerts that obscure legitimate risks to data, and they get burned out trying to chase them all down. Code42 is addressing this problem head on. To protect data from insider threats, security teams need high-fidelity risk detection that cuts through the noise – this is what we call signal. Sharpening signal helps security teams quickly prioritize user activities that need investigation. We believe Code42 is delivering the richest, most prescriptive data security signal on the market today.”
New Risk Indicators
Our new high-fidelity risk indicators filter out non-threatening activities to flag and prioritize high-risk data exposure events. The highlighted events represent real threats that require security investigation. The new capabilities expose:
- File mismatch risk –Identifies when a file’s content type does not match its stated extension, which may indicate internal attempts to maliciously conceal data exfiltration. For example, an employee renames a financial spreadsheet as “FamilyPhotos.jpg.”
- Off-hours activity risk – Tracks employee behavioral patterns to surface file activity that takes place at unusual times. This capability was built with the understanding that work activity – especially now – isn’t confined to a regimented 9-5 workday. It does not require security admins to manually input employees’ regular hours. Rather, it is modeled after an individual’s typical activity and will adapt over time to accommodate sustained adjustments in active hours.
- Remote workforce file activity – Offers a company-wide view of all data exposure and a segmented view of file risks caused by remote employees, as determined by IP addresses.
- Unsanctioned file activity – Enables security teams to remove excessive notifications of trusted domains and URLs from dashboard views and alerts so they can focus on riskier file activity, like uploads to personal Dropbox accounts or email attachments sent to untrusted recipients.
The Risk Indicators at Work
These new indicators shown below are now part of Code42’s user profiles. When high-risk events occur, they are flagged with a yellow diamond.
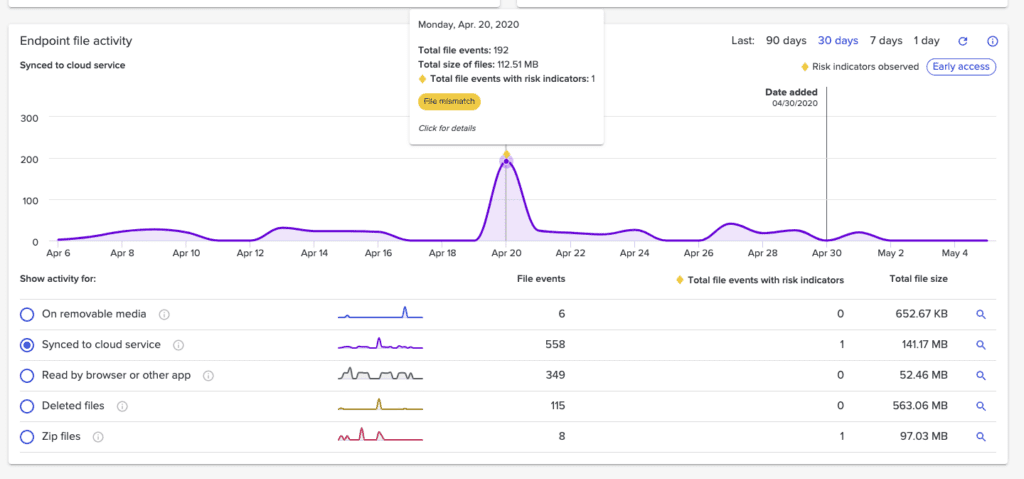
The security team can click into the indicator to investigate and see the file’s history.
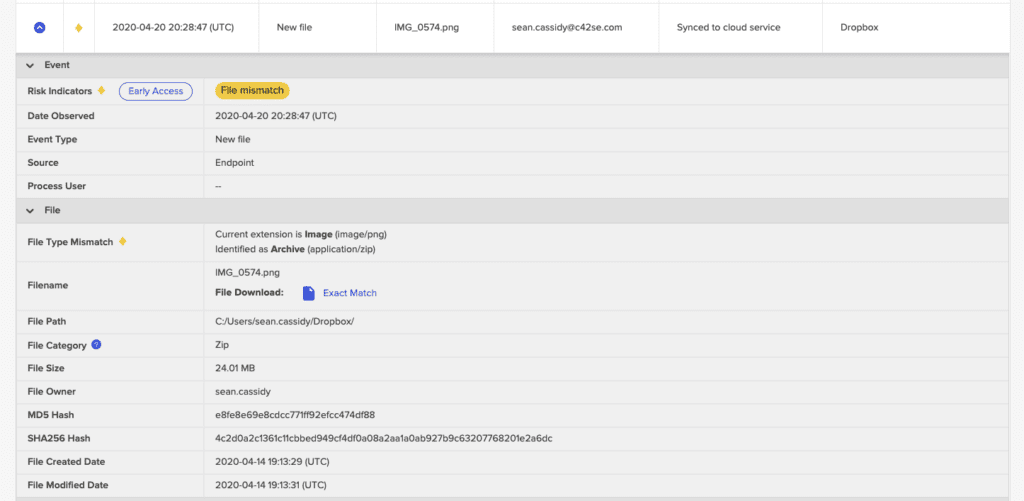
The security team at Code42 is already finding value in the new risk indicators, especially when it comes to file mismatch risk. Austin Wolf, Code42’s information security analyst, explains how reassuring it is when they are sorting through files to know – with confidence – that if a file doesn’t have a flag next to it, the file extension hasn’t been changed. Fellow information security analyst Brandon McHugh agrees that having visual alerts that draw the eye to anomalies makes their job easier, especially when investigating large volumes of files under a user. Previously, the team would have to look at the history of every file in order to spot a file mismatch. That’s not the case any longer.
Brandon also called out how helpful it has been to be able to filter out file activity involving trusted domains and URLs. That way, only the files that are uploaded to unknown or untrusted URLs are the ones revealed in dashboards and alerts. For many teams using tools like Cisco Umbrella, security knows when users visit certain sites, like Evernote for example, but security may not know when a file is uploaded there. Code42 provides the risk signal to prioritize actions like these, which may have been missed before.
Check out the new risk indicators for yourself! Our monthly Code42 in 2 video features this and other new updates:
