The results are in from a survey we conducted at our inaugural Insider Risk Summit. We asked this year’s virtual attendees for their thoughts on how their organizations detect and respond to insider risks. As we reflect on the changes to workplaces and data security in 2020, here are some of the main takeaways from this sample of the security community, coming down to the what, when, and how of insider risk.
What data is important?
When asked to rank the IP and trade secrets most important to their businesses, attendees named customer lists, source code, product strategy, and operational process documentation as some of their top IP. When ranking their top three, a combination of these options was at the top of each list. Respondents have a reason to protect this important information — these types of business documents and source code made up 45% of monthly file movements in our insider risk product, Incydr.

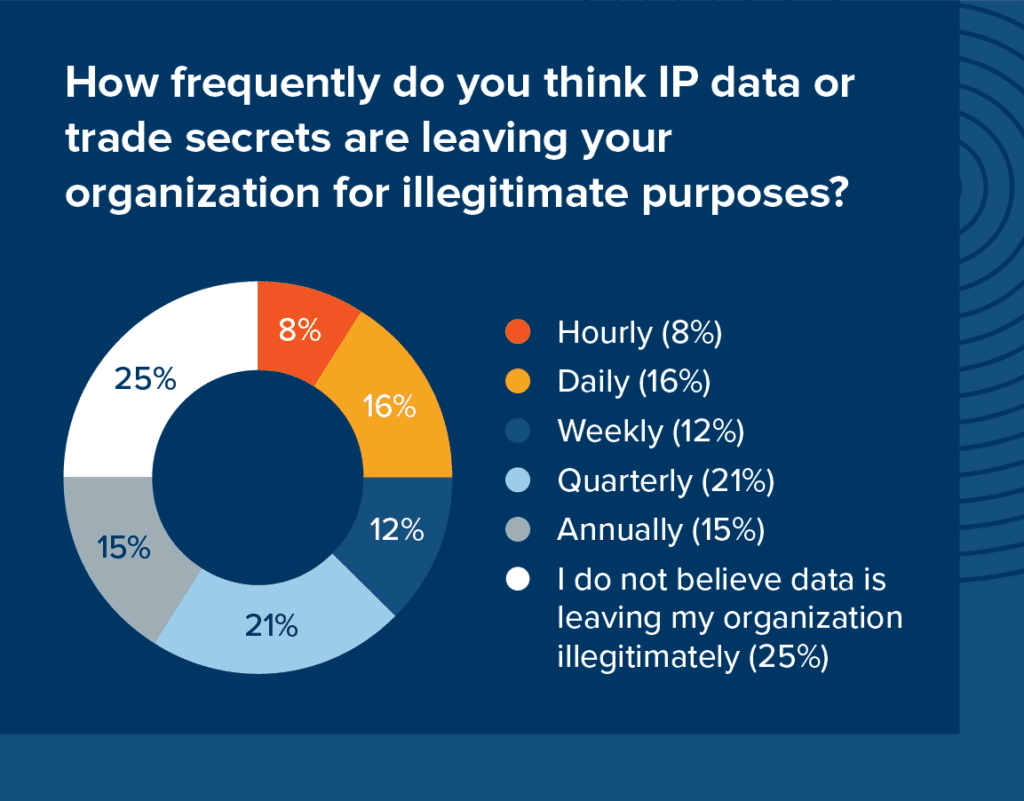
When is data leaving?
Given we know that 66% of data breaches involve an insider, it was surprising to see that 25% of respondents did not believe data was leaving their organizations illegitimately at all. For those who did think data was leaving, 21% stated this was occurring on a quarterly basis and 16% said on a daily basis. These results show us that there is room for improvement in the transparency of how and where data is moving within, and possibly outside, companies. Incydr telemetry data showed that the typical employee causes 20 file exposure events per day.
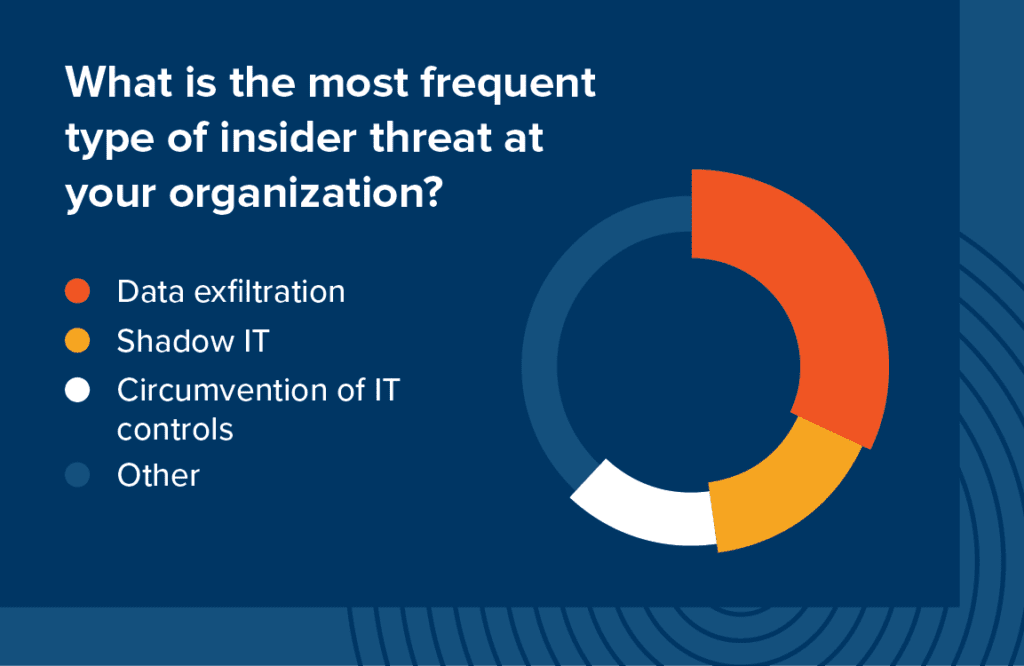
How is data leaving?
When asked to rank the most frequent type of insider risk, respondents most often had data exfiltration, shadow IT, circumvention of IT controls, and privilege misuse in their top 3. It’s important to note that intent is not reflected in these risks– they can happen during a normal workday and can be unintentional. Having the right alerts and context can help security teams prioritize these insider risk indicators.
Looking towards 2021, Forrester predicts an increase in insider incidents, largely due to the continuation of remote work and job insecurity. The survey results from the Insider Risk Summit confirm that organizations are aware of the risks to their data, and that file movements are happening every day.
If you couldn’t join us for our inaugural Insider Risk Summit, a selection of the sessions are now available to view on YouTube. Check them out for expert perspectives on CISO priorities, the psychology of insiders, building an insider threat program and more.
We also recommend:
Pulse Survey: Security Leaders Know Insider Risk is a Major Problem, But Most Aren’t Monitoring It
3 New Priorities That Highlight Why Your Security Stack Might Have Gaps
