Apple released the new macOS Catalina on October 7, setting IT and security teams abuzz about the logistics of upgrading their users, excitement about new features and concerns about the pains that always come with change. But security experts have revealed a troubling impact: macOS Catalina entirely disallows kernel extensions (kexts). This isn’t just another instance of “kernel panic” — this is a full-blown kernel crisis: Legacy DLP products will cease to work in the Mac environment going forward.
Catalina goes
read-only — disallows kexts
With the release of Catalina, Apple shifts the entire macOS to read-only, regardless of permissions. Kernel extensions are completely disabled. This change strengthens the overall security stance of the macOS. But it’s a major problem for legacy DLP products like Symantec and McAfee, which depend on kernel extensions for their core functionality.
Legacy DLP simply
won’t work in Catalina
Disallowing kernel extensions disables the blocking functionality of legacy DLP products. The products will technically still “run” on Catalina (with the usual kernel panics and other pains), but they’ll no longer be able to work the way they have — no more blocking risky user actions. In effect, legacy DLP will cease to work altogether. At a time when insider threat continues to escalate, companies simply can’t afford to risk leaving their data exposed.
You can’t afford not
to upgrade
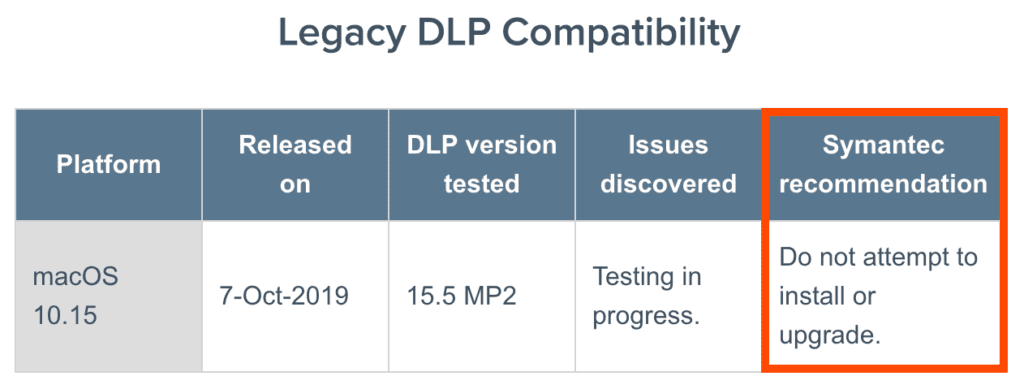
Most legacy DLP vendors are approaching the kernel crisis carefully. They’re reaching out to customers with one-to-one communications, trying to convince them not to upgrade to Catalina so they can retain the functionality of their DLP products (for example, reference the table on Symantec’s support page). But not upgrading is not viable in the long-term. You need to give your users access to the latest features of Catalina; moreover, your users will demand the upgrade. And your security team can’t afford the security risks of lagging behind.
There’s not a ton of time to waste, either. Apple will end updates, security patches and support of macOS Mojave in less than 24 months. That means most organizations need to begin planning their upgrades — including how they’ll fill the enormous security gap — now.
DLP for Macs has
always been painful
Running legacy DLP on
macOS has always been frustrating—a “square-peg-round-hole” problem that
creates more work for security teams and increases the potential for dangerous
gaps in visibility and protection. But the clear trend is that Apple is making
it even harder for DLP to function in macOS — leading to more kernel panics,
frustrations and potential security gaps. So the “kernel crisis” of the
Catalina upgrade isn’t coming out of nowhere. The reality is that legacy DLP
was not built with Macs in mind, and this disconnect is coming to an urgent
head.
Code42 is data risk detection and response built for Macs
At Code42, we know the pains of legacy DLP for Macs firsthand — and built our Code42 Incydr™ solution to mesh seamlessly with macOS. We understand macOS better, so we approach things differently by:
- Working at the file-system level to focus on
what really matters — your file data - Monitoring the applications that access,
interact with and touch those files - Giving you deeper, broader visibility into all
file activity — across your endpoints, in the cloud and in applications
We don’t have to muck around at the kernel level, playing the whack-a-mole game of activity-blocking. All of this means that the robust functionality of Incydr is completely unimpacted by the security improvements of the Catalina upgrade.
Providing the business-critical push to move to a new data risk protection solution
Most security pros already know the many pains of running legacy DLP products on Macs. So, the good news is that the Catalina kernel crisis will give many security teams the final push they need, providing a business-critical reason to move to a better data loss protection solution. In fact, several of the world’s leading tech companies anticipated the Catalina kernel crisis and have turned to Code42 Incydr.
